What is Splunk
Splunk is a machine data analytics platform used to collect, index, search, and visualize large volumes of log data.
Organizations use Splunk to monitor:
- Applications
- Servers
- Security events
- Network devices
- IoT systems
Key Functions
- Collect Data
- Index Data
- Search Data
- Analyze Data
- Visualize Data
2. Splunk Products
1. Splunk Enterprise
- On-premise platform
- Full features
2. Splunk Cloud
- SaaS version
- Managed by Splunk
3. Splunk Light
- Small scale log management
4. Splunk Enterprise Security (ES)
- Security monitoring platform
5. Splunk ITSI
3. Splunk Architecture

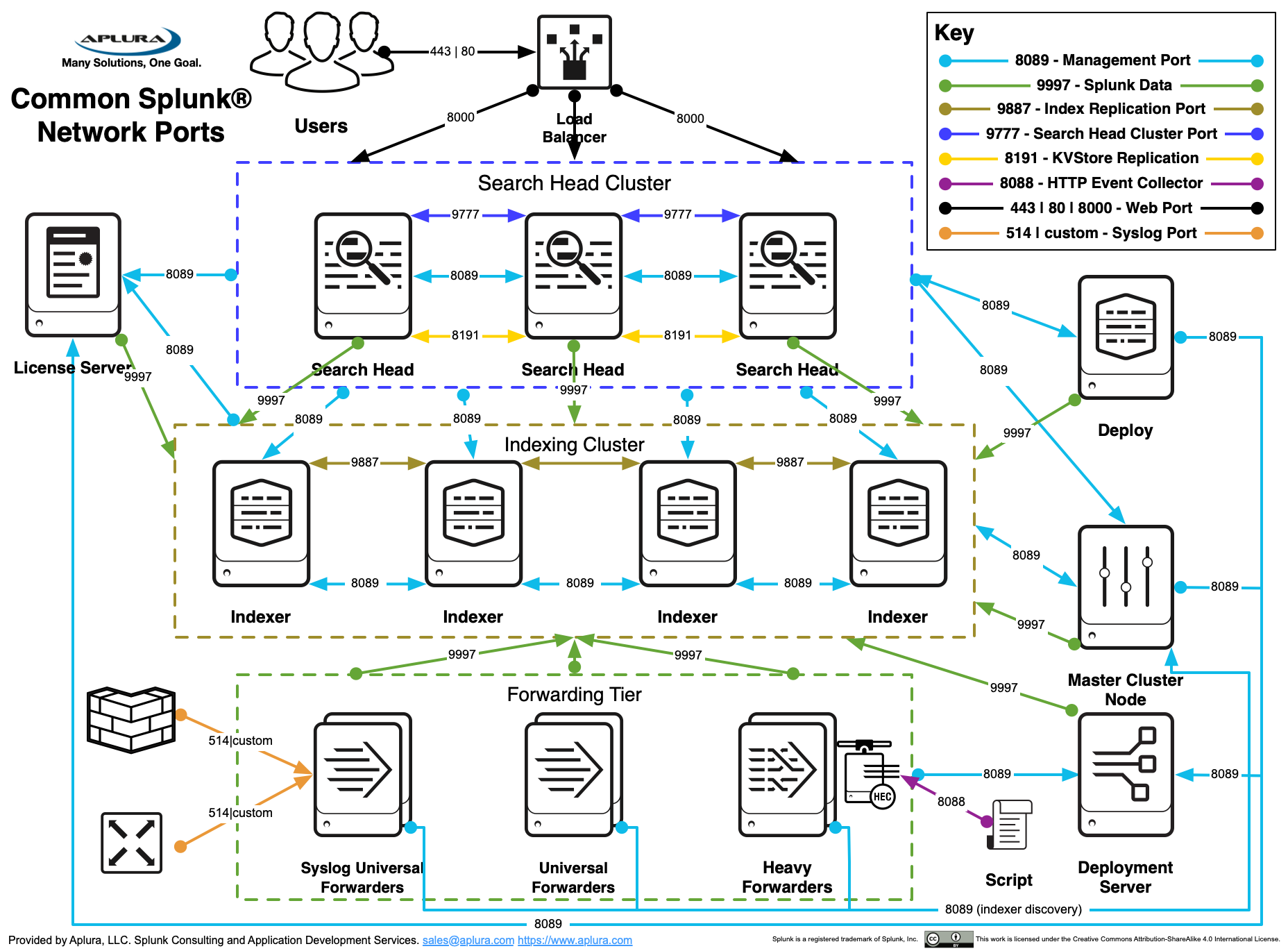

Core Components
Forwarder
Collects logs and sends them to Splunk.
Types:
- Universal Forwarder
- Heavy Forwarder
Indexer
Stores indexed data and processes searches.
Search Head
Runs search queries and generates dashboards.
Deployment Server
Manages forwarders.
License Master
Controls license usage.
4. Splunk Installation
Requirements
- Linux / Windows
- Minimum 8GB RAM recommended
Installation Steps
- Download Splunk
- Install package
- Start Splunk
Command:
Web Interface
5. Data Ingestion
Splunk collects data from multiple sources.
Types of Inputs
| Input Type | Example |
|---|
| File monitoring | /var/log/syslog |
| Network data | TCP / UDP |
| Scripted inputs | Python scripts |
| APIs | REST APIs |
| HTTP Event Collector | HEC |
Example:
6. Source Types
Source types define format of data.
Examples:
- syslog
- apache_access
- mysql_error
- log4j
Purpose:
- Proper timestamp detection
- Field extraction
- Event parsing
7. Splunk Indexes
Index is where Splunk stores data.
Default indexes:
| Index | Purpose |
|---|
| main | default logs |
| _internal | Splunk internal logs |
| _audit | audit logs |
Example index creation:
8. Search Processing Language (SPL)
SPL is used to search data.
Basic syntax:
Example:
9. SPL Commands (Important)
Filtering
Stats Command
Chart Command
Timechart
Top Command
Sort
10. Fields in Splunk
Fields are extracted from events.
Examples:
- host
- source
- sourcetype
- timestamp
Field Extraction
Example:
11. Knowledge Objects
Knowledge objects enrich data.
Types:
- Fields
- Tags
- Event Types
- Lookups
- Macros
- Workflows
- Reports
- Dashboards
12. Lookups
Lookups add extra data.
Example:
| IP | Country |
|---|
| 1.1.1.1 | USA |
| 2.2.2.2 | India |
Example SPL:
13. Reports
Reports are saved searches.
Example:
Daily error report.
Features:
- Scheduled execution
- Shareable
- Exportable
14. Dashboards